A step by step guide to build a Windows Server 2019 Remote Desktop Services deployment.
I posted this before based on Windows Server 2012 R2 RDS and thought it was high time to update this post to a more modern OS version.
I will provide all the steps necessary for deploying a single server solution using the GUI tools.
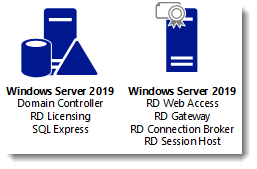
Although it is called a single server installation, we will need 2 servers as shown below.
Software used in this guide:
Windows Server 2019 ISO (evaluation can be downloaded here: https://www.microsoft.com/en-us/evalcenter/evaluate-windows-server-2019).
SQL Server 2017 Express x64 (free version can be downloaded here: https://www.microsoft.com/en-us/download/details.aspx?id=55994).
SQL Server 2016 Native Client (free version can be downloaded here: https://www.microsoft.com/en-us/download/details.aspx?id=52676. After clicking the download button select ENU\x64\sqlncli.msi). Although I’m installing SQL Express 2017, there are no newer client tools available.
SQL Server Management Studio (free, and can be downloaded here: https://docs.microsoft.com/en-us/sql/ssms/download-sql-server-management-studio-ssms).
And a certificate. I got mine for free from https://www.sslforfree.com/. This certificate needs to contain the FQDN you will use as the RD Web Access URL (mine is rds.it-worxx.nl in this guide). It needs to be in .pfx format and you need to have the private key in it.
This guide will not focus on building a domain using a single domain controller and adding the second server as a member server to this domain.
Also some basic knowledge is assumed in this guide. I will not detail how to create a Security Group and adding a computer account to it. I will also not detail how to install SQL Express, or adding logins to a SQL Server Instance security context. If you need extra help with this, Bing it or drop me a mail with details, and I will provide steps to continue.
I will be using Hyper-V on my Windows 10 1809 laptop and I have prepared 2 servers:
ITWDC (1 vCPU, 1024MB memory, dynamic, 60GB Harddisk)
Installed Windows
IPv4 192.168.0.4/24
Added .NET Framework 3.5 as a feature
Added Active Directory Domain Services as a role
Configured this server as a Domain Controller in a new forest: it-worxx.lab
ITWRDS (1 vCPU, 1024MB memory, dynamic, 60GB Harddisk)
Installed Windows
Added .NET Framework 3.5 as a feature
IPv4 192.168.0.10/24, DNS server 192.168.0.4
Configured it as a member server in the it-worxx.lab domain
Installing the Remote Desktop Services Roles
Log on to the Domain Controller, and in Server Manager right-click the All Servers node and add the second server using the Add Servers command (or select the All Servers node, click Manage and click Add Servers).
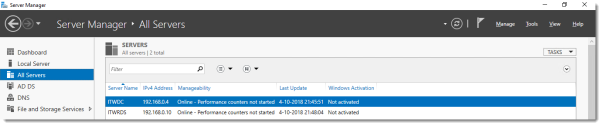
Now that all servers needed in this deployment scenario are present, click Manage, and click Add Roles & Features.
Before you begin
Click Next.
Select Installation Type
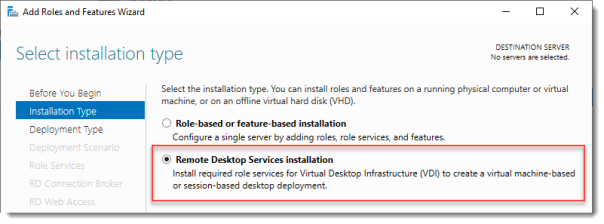
Select Remote Desktop Services installation.
Click Next.
Select Deployment Type
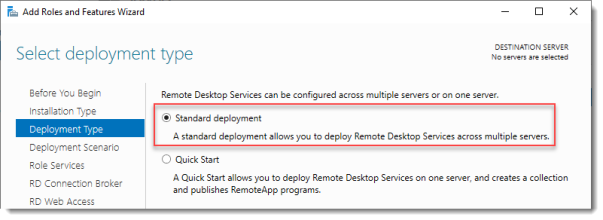
Although Quick Start might be a valid option for a single server deployment, leave the default selected. This will explain the steps necessary to install Remote Desktop Services in greater detail.
Click Next.
Select Deployment Scenario
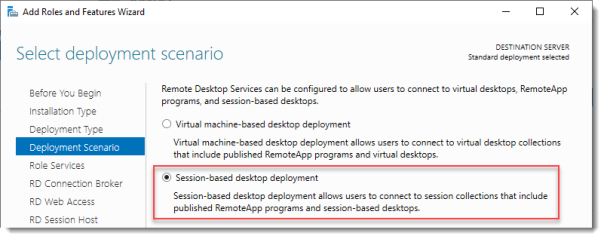
Select Session-based desktop deployment.
Click Next.
Review Role Services
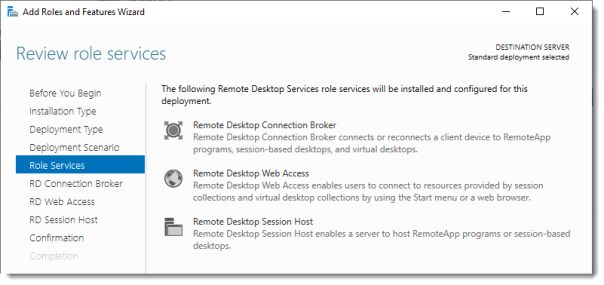
Review the services that will be installed.
Click Next.
Specify RD Connection Broker server
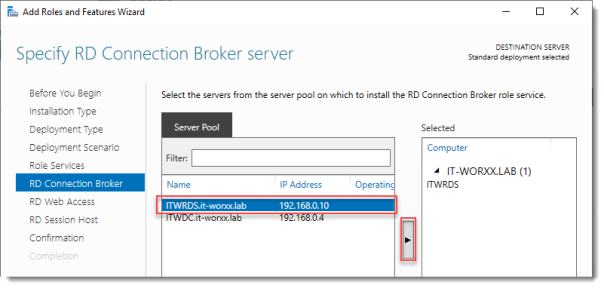
Click the member server and click the Add button.
Click Next.
Specify RD Web Access server
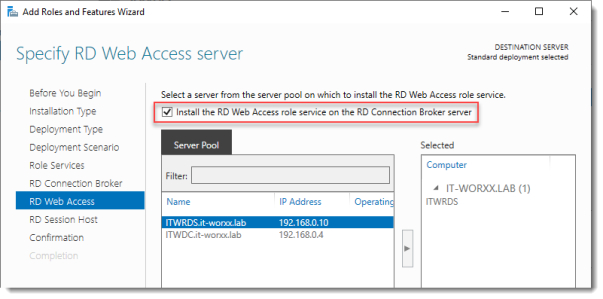
Check Install the RD Web Access role on the RD Connection Broker server.
Click Next.
Specify RD Session Host server
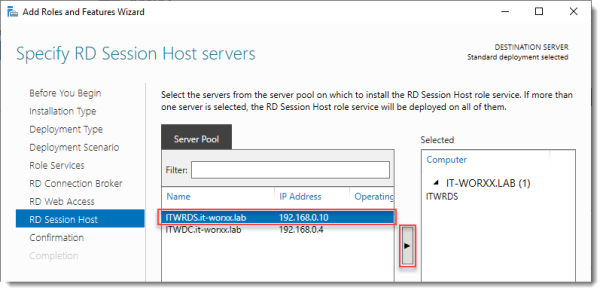
Click the member server and click the Add button.
Click Next.
Confirm selections
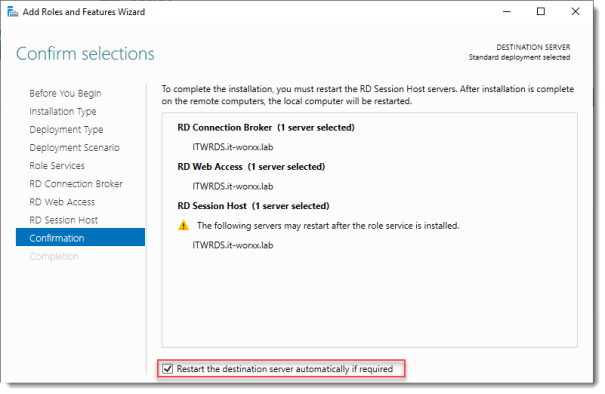
Check Restart the destination server automatically if required.
Click Deploy.
View progress
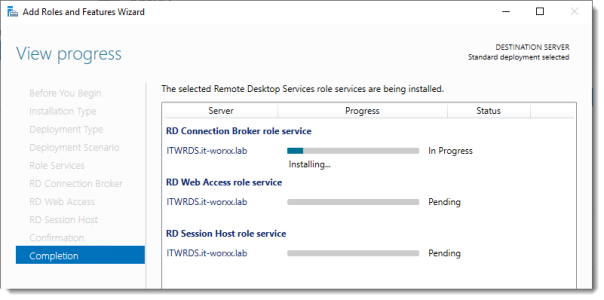
Wait until all role services are deployed and the member server has restarted.
Click Close.
In Server Manager click Remote Desktop Services and scroll down to the overview.
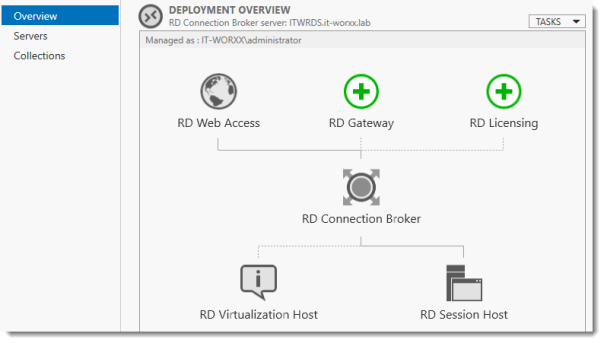
As you can see the deployment is missing a RD Gateway server and a RD Licensing server.
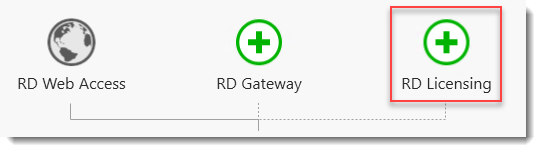
Click the Add RD Licensing server button.
Select a server
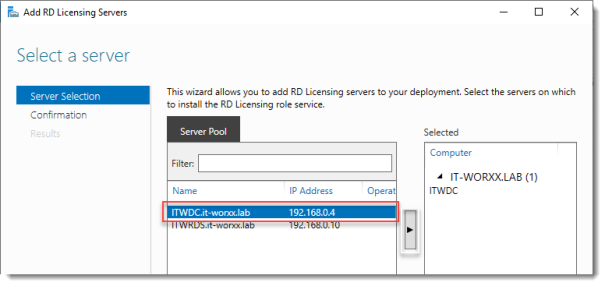
Click the domain controller and click the Add button.
Click Next.
Confirm selections
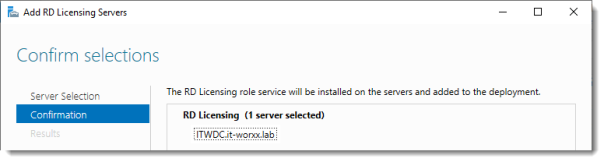
Click Add.
View progress
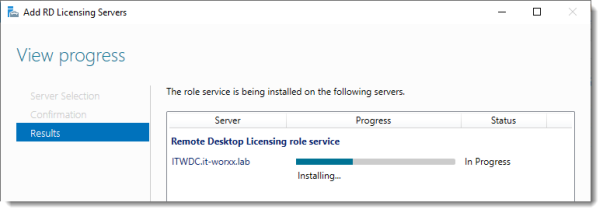
Wait until the role service is deployed. No restart is needed.
Click Close.
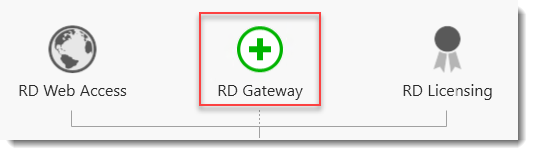
Click the Add RD Gateway server button.
Select a server
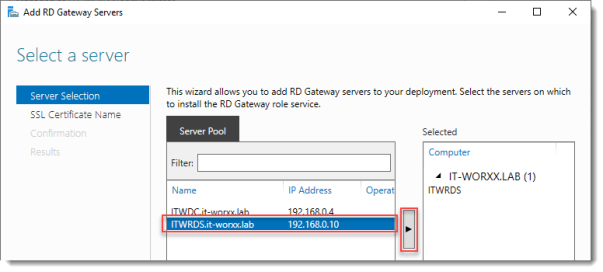
Click the member server and click the Add button.
Click Next.
Name the self-signed SSL certificate
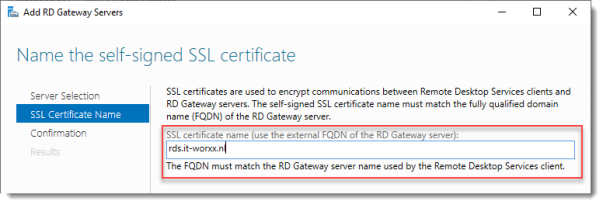
The wizard creates a self-signed certificate. We will deal with certificates in this deployment in a little bit. We will replace the self-signed certificate.
Enter the external Fully Qualified Domain Name which you will also use for the Web Access URL. In my case, for lack of a better name, I used “rds.it-worxx.nl”. I didn’t want to use “remote.it-worxx.nl” or “desktop.it-worxx.nl” or anything else.
Click Next.
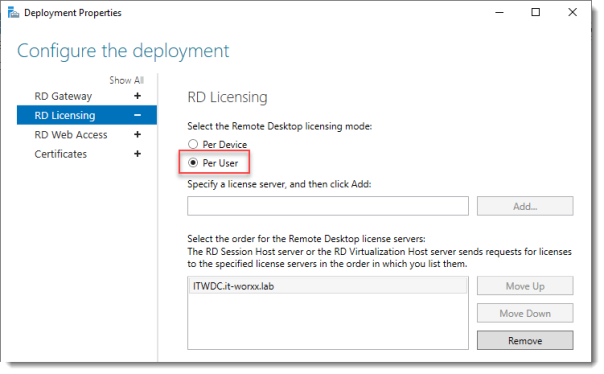
Confirm selections
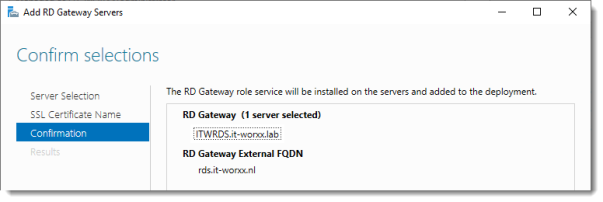
Click Add.
View progress
Wait until the role service is deployed. Again, no restart is needed.
Notice that “rds.it-worxx.nl” was configured for the deployment.
Also notice that even more certificate configuring is needed, but we’ll get to that later. Pay no attention to it for now. The same goes for the RD Gateway properties for the deployment. We’ll get to that later.
Click Close.
Review role installation and setting License Mode
Let’s have a quick look at the configuration we have so far.

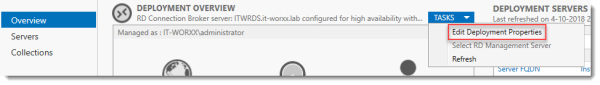
In Server Manager, Remote Desktop Services, Overview, click Tasks and click Edit Deployment Properties.
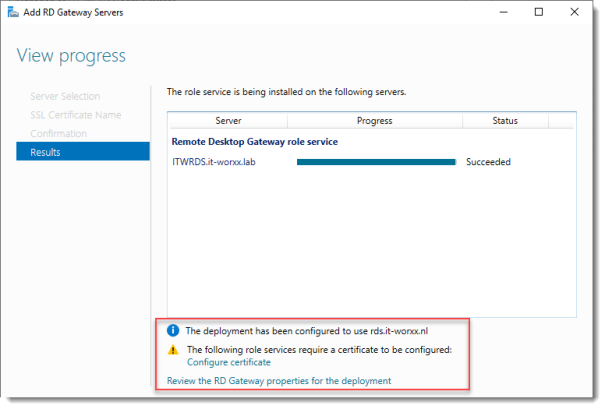
Configure the deployment
Review the RD Gateway settings and notice what settings are available.
Click RD Licensing.
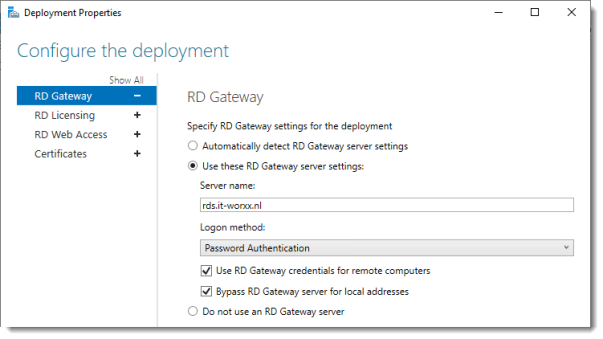
Configure the deployment
Notice that an RD License server is available, but no license type is selected yet.
I selected Per User, but since this is just a guide setup, it really doesn’t matter.
Click RD Web Access.
Configure the deployment
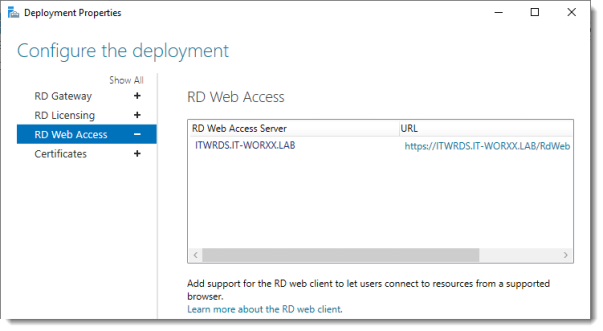
By default the RD Web Access IIS application is installed in /RdWeb.
If you want to know how to change this, check another post: https://msfreaks.wordpress.com/2013/12/07/redirect-to-the-remote-web-access-pages-rdweb/
This is for Windows Server 2012 R2 RDS, but it also works for Windows Server 2019 RDS.
Click Certificates.
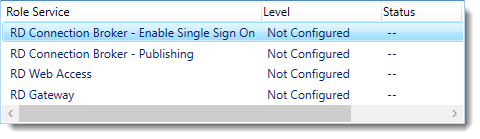
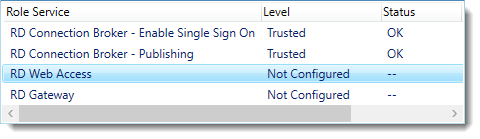
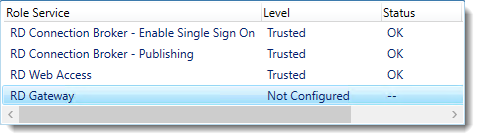
Configure the deployment
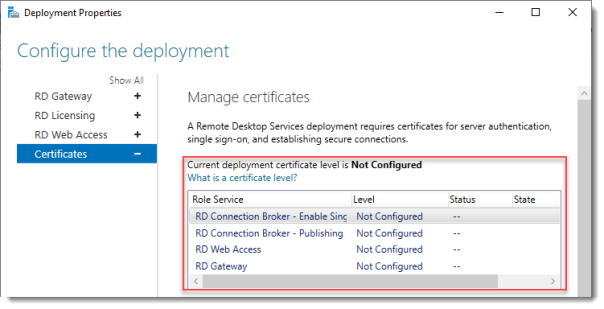
Notice that the certificate level currently has a status of Not Configured.
As you can see, certificates are used for different goals within the deployment.
The RD Gateway certificate is used for Client to gateway communication and needs to be trusted by the clients. Either install the self-signed certificate on all clients, or use a certificate for which the complete certificate chain is already trusted by all clients. As it said in the wizard, the external FQDN should be on the certificate.
The RD Web Access certificate is used by IIS to provide a server identity to the browser clients.
The RD Connection Broker actually has two goals for which it needs certificates. To enable single sign on (server to server authentication), and for publishing (signing RDP files). If you look in the deployment you’ll see that the Connection Broker is now configured to use “itwrds.it-worxx.lab”, so we have to change it to use an external FQDN as well.
If we use the same FQDN for all goals described above, we need only 1 certificate, and only 1 external IP address.
We’ll come back to this wizard later to assign the certificate. First order of business is to change the internal FQDN for the Connection Broker to an external FQDN.
Click OK (no reason why we shouldn’t commit the change we made on the licensing tab, remember?)
Changing the Connection Broker FQDN to an externally resolvable FQDN
Open DNS Manager on the domain controller and browse to Forward Lookup Zones.
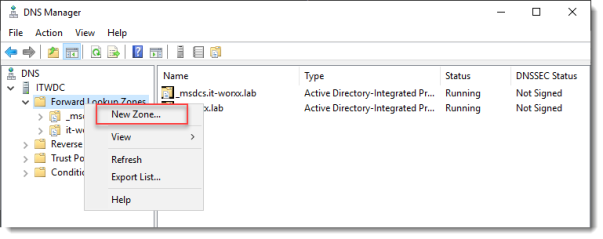
Right click Forward Lookup Zones and click New Zone… Go through this wizard accepting the defaults until you have to enter a Zone Name.
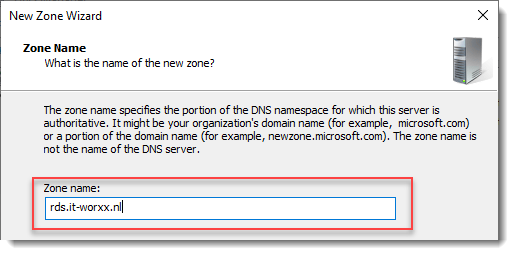
Enter the external FQDN which will also be used by the Connection Broker.
Finish the rest of the wizard accepting the defaults.
Browse to the newly created zone.
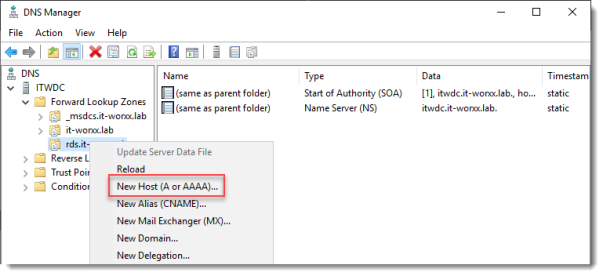
Right click the newly created zone and click New Host (A or AAAA)…
New Host
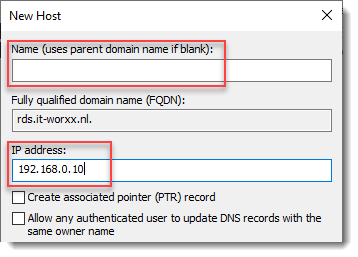
Leave the Name field blank, but enter the member server’s (holding the RD Connection Broker role) IPv4 address.
Click Add Host.
Now the configuration will be able to resolve “rds.it-worxx.nl” to the server holding the Connection Broker role, and this will work because “rds.it-worxx.nl” is also on the certificate that we will configure later.
Create a new Global Security Group called “RD Connection Brokers” and add the computer account for the member server to it as a group member.
We need this group to be able to convert the RD Connection Broker to a highly available RD Connection Broker. You’ll see why we need to do this in a few steps.
Reboot the member server to let it know it’s a member of the RDS Connection Brokers security group.
The next steps in re-configuring the RD Connection Broker depend on an SQL database shared by all Connection Brokers in the deployment. Without this configuration the RD Connection Broker will rely on the Windows Internal Database that was created during the initial deployment of the roles.
Install SQL Express on the Domain Controller (or use an existing SQL Server if you already have one).
It’s not best practice to install SQL onto a Domain Controller, but it’ll do for this guide.
Here’s a list of needed features:

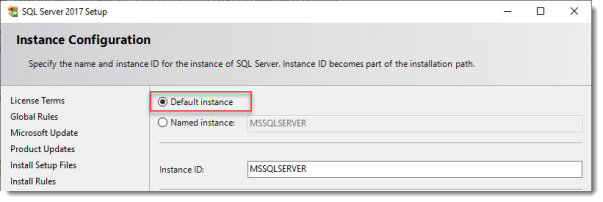
Use the Default Instance (so click Default, and do not leave the wizard’s selection on Named instance: SQLEXPRESS).
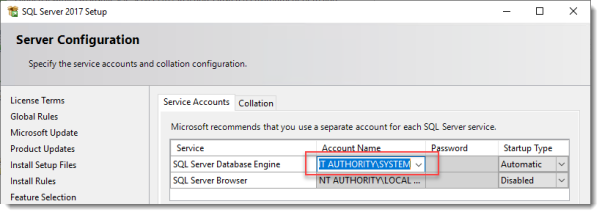
Set the SQL Service to start using SYSTEM because the default account of SQLSERVER cannot be used on a Domain Controller.
When the installation is done open SQL Configuration manager and browse to Client Protocols under SQL Native Client 11.0 Configuration.
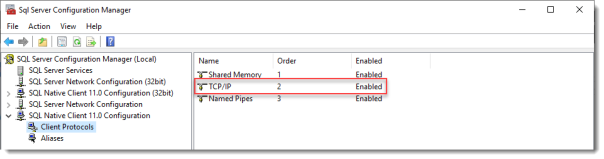
Check if TCP/IP is enabled under Client Protocols. SQL Express install enables this by default, but check it just to be sure, especially if you use an existing SQL Server.
Browse to Protocols for MSSQLSERVER under SQL Server Network Configuration.
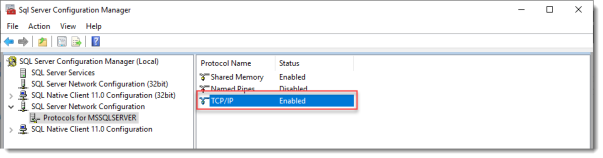
Enable TCP/IP. If this is a new SQL installation, this will be disabled by default.
Restart the SQL Server service if you changed this setting.
On the SQL Server, make sure port 1433 is not being blocked by Windows Firewall.
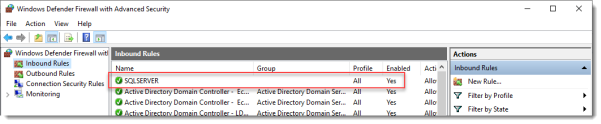
I added the SQL Server executable to the exception list to allow all inbound traffic, but TCP 1433 inbound should suffice.
If you installed SQL Server using the default folder locations, the sqlservr.exe executable is found in “C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\Binn”.
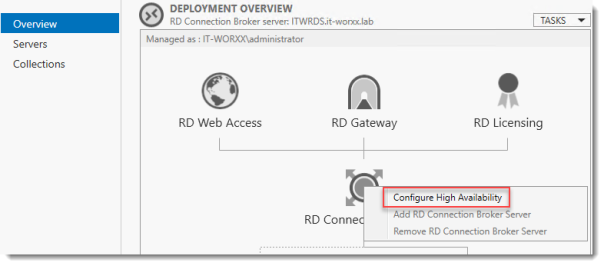
Open SQL Server Management Studio, connect to the default instance on the Domain Controller and browse to Logins under Security.
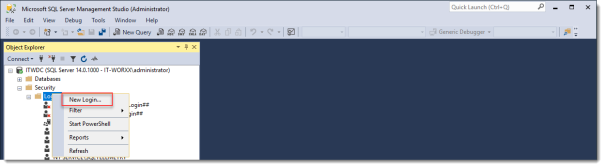
Remember the Management Studio is no longer available with the SQL Server download, but is a different download.
Right click Logins and click New Login…
Login – New
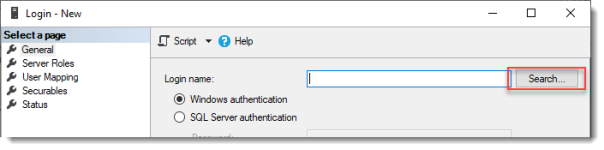
Click Search…
Select User, Service Account, or Group
Click Object Types… and select Group.
Type the RDS Connection Brokers security group name and click Check Names.
Click OK.
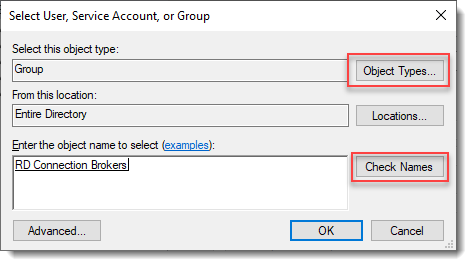
Login – New
Click Server Roles and select dbcreator.
Click OK.
We have just effectively granted the RDS Connection Broker server the right to create databases.
We need this because the RDS Connection Broker service will try to migrate from WID (Windows Internal Database to a (high available) SQL Server instance when we convert the Broker to a high available broker.
Install the SQL Native Client on the member server (Client Components only). If you used the member server in this setup to install the SQL Management Studio, you can skip this step because the Native Client was installed with installing the Management Studio.
Everything we need is in place to convert the RD Connection Broker, so let’s do just that.
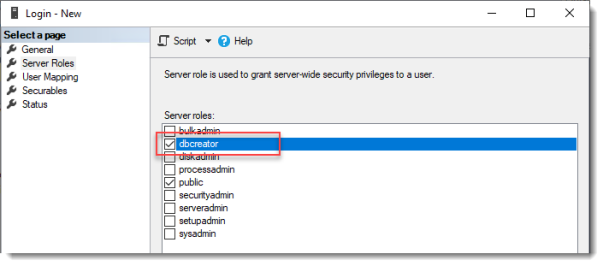
In Server Manager click Remote Desktop Services and scroll down to the overview.
Right click RD Connection Broker and click Configure High Availability.
Before you begin
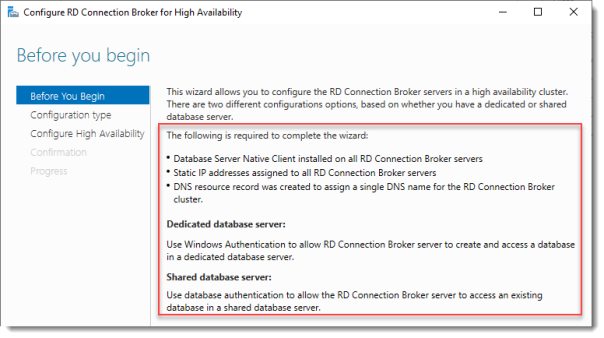
So we’re building a single node cluster here ;)
Look at the pre-requisites.
If you have more than one RD Connection Broker they need to be configured using DNS Round Robin.
Click Next.
Configure RD Connection Broker for High Availability
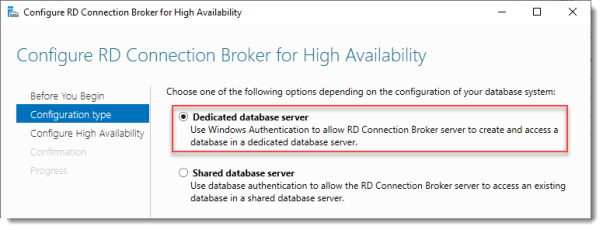
Since we just installed an SQL Server for this, leave the default selected. You’d use the other option for instance if you’d like to use Azure SQL for this deployment.
Click Next.
Configure RD Connection Broker for High Availability
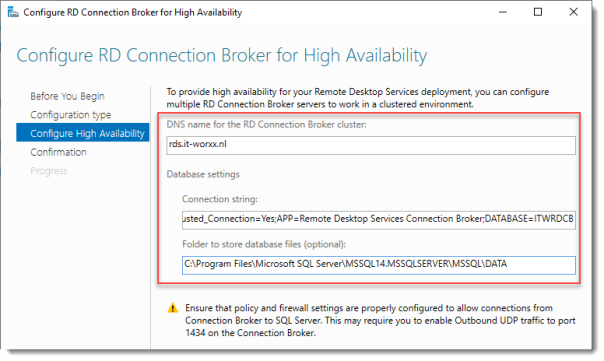
DNS name for the RD Connection Broker cluster:
The DNS Zone name we configured in DNS earlier: rds.it-worxx.nl
Connection string:
DRIVER=SQL Server Native Client 11.0;SERVER=ITWDC;Trusted_Connection=Yes;APP=Remote Desktop Services Connection Broker;DATABASE=ITWRDCB
Folder to store database files:
C:\Program Files\Microsoft SQL Server\MSSQL14.MSSQLSERVER\MSSQL\DATA
I used the instance default folder.
Click Next.
Confirmation
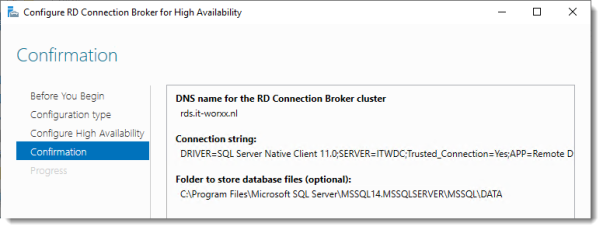
If you get an error before this page:
- Check if TCP/IP is enabled in client protocols and for your instance
- Check if you can reach port 1433 on the SQL Server from the member server
Click Configure.
Progress
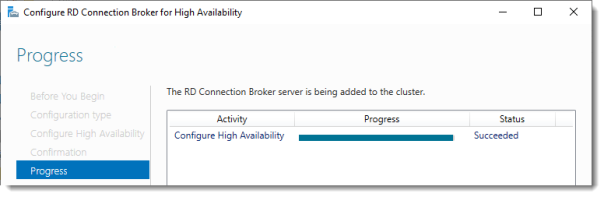
If you get an error on this page:
- Check SQL permissions for the security group
- Check if the database path you entered is correct
Click Close.
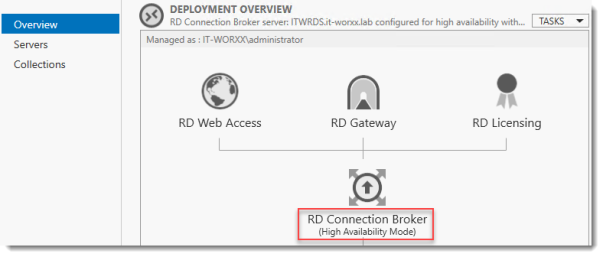
The RD Connection Broker is now in High Availability Mode, and configured as “rds.it-worxx.nl” and we are finally ready to complete the configuration.
Configuring Certificates
In Server Manager, Remote Desktop Services, Overview, click Tasks and click Edit Deployment Properties, then click Certificates.
Configure the deployment
Click RD Connection Broker – Enable Single Sign On and click Select Existing certificate.
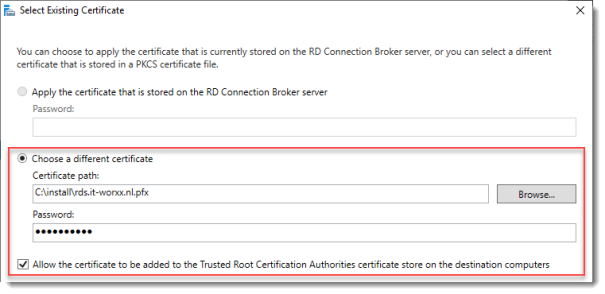
Browse to the .pfx file, enter its password, and check Allow the certificate..
Click OK.
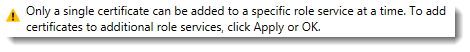
So click Apply. This takes a little while, be patient.
Configure the deployment
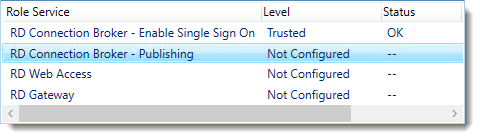
Click RD Connection Broker – Publishing and click Select Existing certificate.
Browse to the .pfx file, enter its password, and check Allow the certificate..
Click OK.
Click Apply. This again takes a little while, be a little more patient.
Configure the deployment
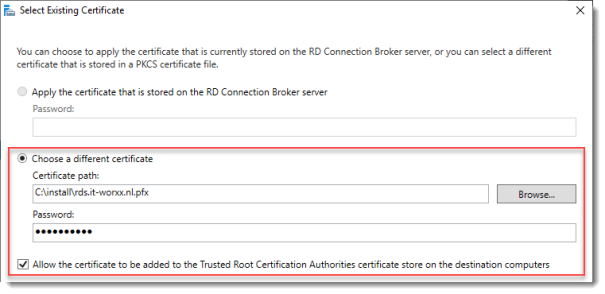
Click RD Web Access and click Select Existing certificate.
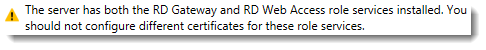
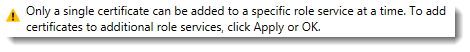
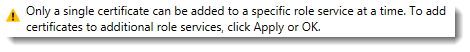
Note: Did you notice the warning when you select RD Web Access?
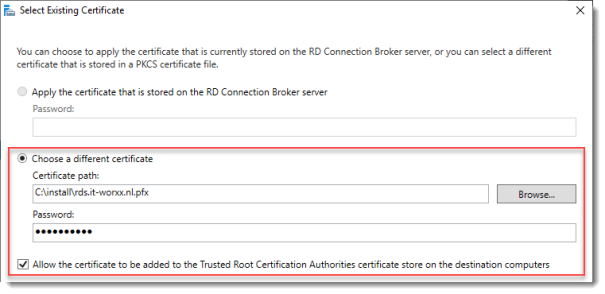
Browse to the .pfx file, enter its password, and check Allow the certificate..
Click OK.
Click Apply again. This takes another little while longer, be slightly more patient.
Configure the deployment
Last one. Click RD Gateway and click Select Existing certificate.
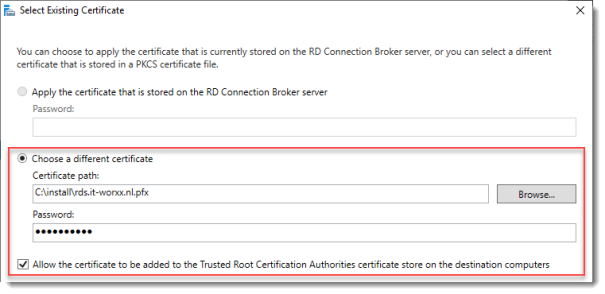
Browse to the .pfx file, enter its password, and check Allow the certificate..
Click OK.
Click OK to apply the final certificate step.
Configured all servers, configured certificates..
One thing left to do: Tell our RDS environment exactly what to publish.
Publishing resources to your users
In fact you can use this setup to either provide full desktop sessions on the Session Host, or you can choose to publish only applications on the Session Host.
Let’s publish full desktop sessions.
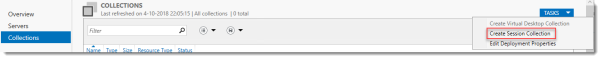
In Server Manager, Remote Desktop Services, Session Collections, click Tasks and click Create Session Collection.
Before you begin
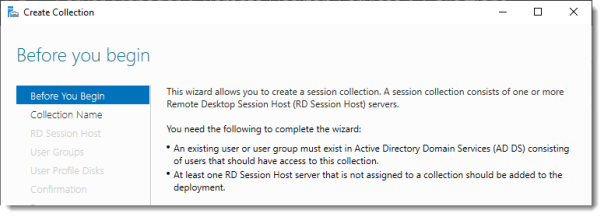
Review the requirements. This won’t be an issue in this setup, but you could restrict access to this collection by selecting a select group of people.
Click Next.
Name the collection
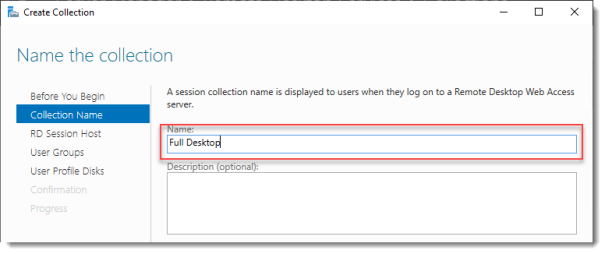
Enter a descriptive name. This name will be displayed under its icon in the Web Access interface.
Click Next.
Specify RD Session Host servers
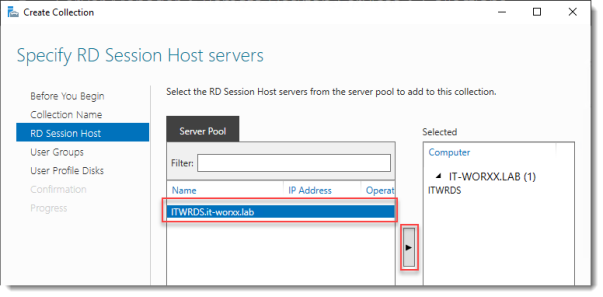
Click the member server and click the Add button.
Click Next.
Specify user groups
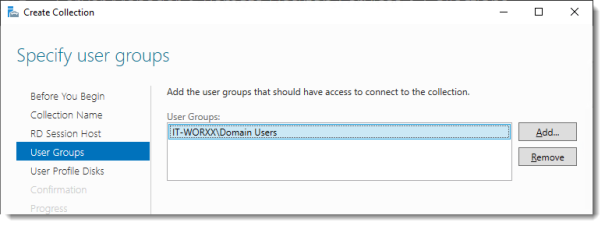
You can limit access to the resource here if you want. Add one or more groups to restrict access to these groups only. In this setup the default selection of Domain Users will do fine. Groups you specify here will be added to the list of groups of users that are allowed to connect using RDP to the Session Host server(s).
Click Next.
Specify user profile disks
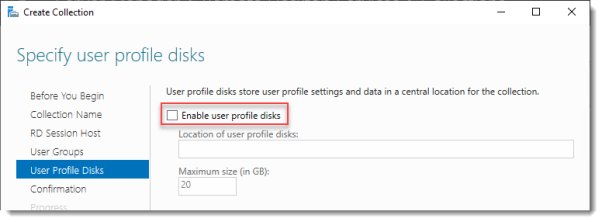
User profile disks are not in focus in this guide. Since I have no file shares configured in this setup, uncheck Enable user profile disks for now.
Click Next.
Confirm selections
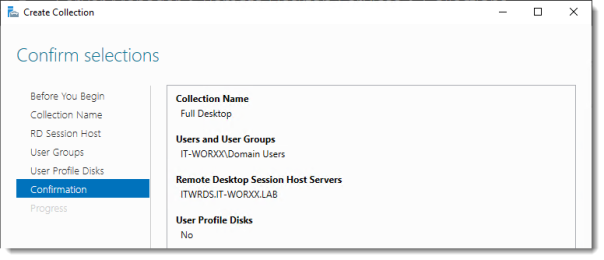
Review the information and click Create.
View Progress
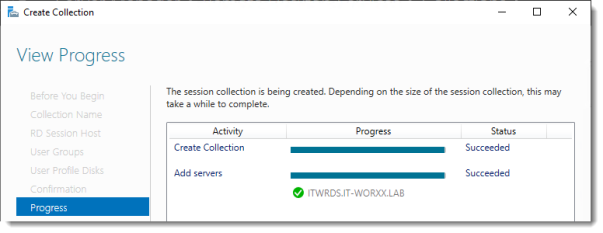
Wait until the collection is created and the server is added to the collection.
Click Close.
Time to test the setup!
Testing the setup
On a machine that has access to your test setup (you may have to add the external FQDN to your hosts file if you didn’t publish it to the internet) open https://rds.it-worxx.nl/rdweb
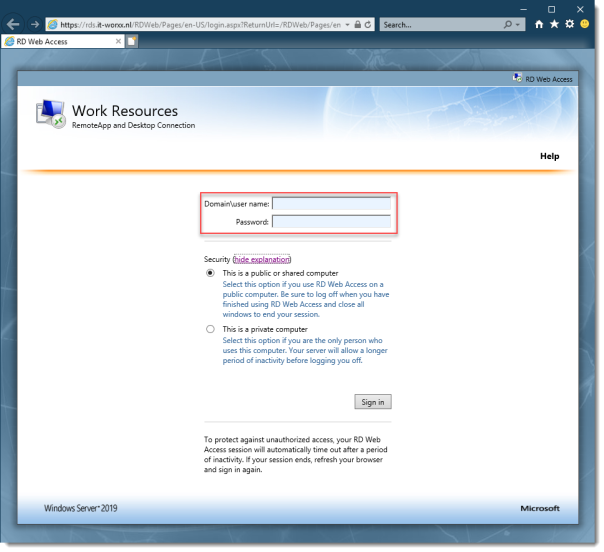
Hey! At least the RD Web Access application works :)
Enter a valid username and password (IT-WORXX\username or username@it-worxx.lab).
Create a user for this, or simply use the domain admin account.
Click Sign in.
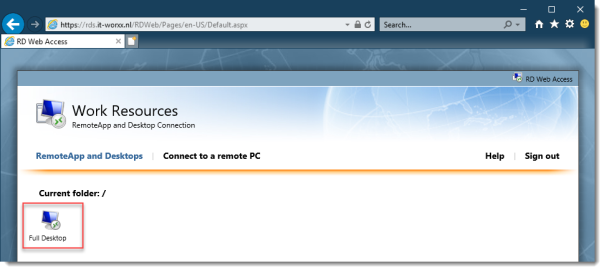
After logging in you are presented with the full desktop session collection we created.
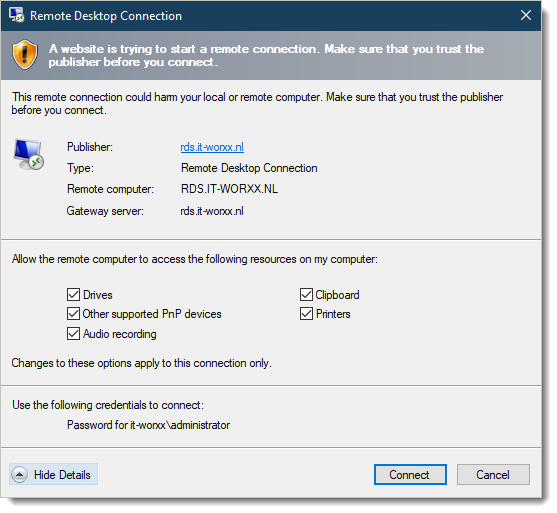
After clicking the Full Desktop icon you get the warning that devices are going to be redirected.
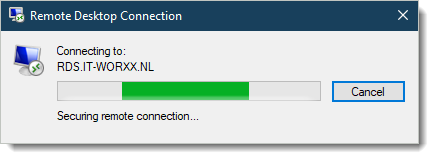
And when you click Connect, you connect :)
Enjoy.
Arjan
Hello Arjan
Thank you for your step-by-step explanation, very helpful.
But I do have a question: what is the purpose to install all those features if it is to finally open port 3389 which is the port of Remote Desktop Connection? If this port is open pointing to the RD Session Host on the firewall, from outside the network, no need to log on the web server, and you just have to launch on the client side a Remote Desktop Connection pointing to the FQDN of the server and that’s it.
For what I read on the following article (best answer), the purpose of installing Remote Desktop Service on servers is also to bypass port 3389, and the process which should be in place should work with only port 443 and 3391 (three three nine one).
https://social.technet.microsoft.com/Forums/exchange/en-US/3ec83740-893d-4165-93d3-4507275dac10/server-2012-remoteapp-custom-port?forum=winserver8gen
“When an external client launches a RemoteApp they will connect to your RD Gateway via TCP port 443 and UDP port 3391, then the RDG will connect to your internal RDSH servers using TCP port 3389 and UDP port 3389 on behalf of the external client. In this way the RDG will act as a middleman between your external users and your internal RDSH servers.”
By the way, I am not able to achieve what is said in this article with ports 443 and 3391, and my client gets the following message
—————————
Remote Desktop Connection
—————————
Your computer can’t connect to the remote computer because the Remote Desktop Gateway server is temporarily unavailable. Try reconnecting later or contact your network administrator for assistance.
—————————
OK Help
—————————
In case you have an idea …
Best
Read up on Remote Desktop Services please.
OK found …
It works with port 443 TCP and 3391 UDP
The message
“Your computer can’t connect to the remote computer because the Remote Desktop Gateway server is temporarily unavailable”
was because the service Remote Desktop Gateway was simply stopped …
Spend hours on this, I feel so stupid …
But is is solved and ut is working now.
Best
Hi
I have RDS running Server 2019. When I try to limit the access to a published app in server manager to a particular user I get an error saying “The security identifier could not be resolved. Ensure a two-way trust exists for the domain of the selected users Exception:The network path was not found” I do not get this error with other Server 2016 servers.
All the servers are running in one domain
To try to fix this error I have done the following:
– logged in as domain admin
– launched server manager “as administrator”
– edited the hosts file so it has the IP addresses of the primary domain controller and this server in both FQDN and non-FQDN forms
Any suggestions ?
Many thanks
I solved my problem so I thought I’d mention how.
In the host file I removed the FQDN for the Domain controller and the FQDN for the server (just leaving the non-FQDN for the two servers itn he hosts file) and then I could apply specific users to certain published apps in RDS.
Thank you very much for helping out with this guide! it mades all a lot easier for me to first time ever get into windows server and remote desktop! in just 1 day I set up all the required servers. with a few issues on the certs but solved that today :)
Now my hyper-v clients can join my hyper-v servers and use remote desktop :D
…and the most important I finally can test and work around with Get-RDUserSession command.
Best wishes,
Paddy
After ‘Confirm Selections’ the install FAILS – because it cant find ntdspers.dll – I have the latest windows update which is supposed to have the ‘fix’ in it. How do I move on from here?
Hello Arjan Mensch,
This is a great article & I was able to configure Remote Desktop service successfully. I my setup I have two servers CB server and Session server.
Do you have a article for setup a VPN server for Server 2019 ?
Is it possible to configure VPN server on the same Connection Broker server ?
Hi Sir I have seen your RD gateway setup . They all are very good and nicely explain. I have setup RDS on my AWS cloud account. I have setup 1 Active Directory on private subnet and RD web access server using quick installation on private subnet and 1 Rd gateway on public subnet. When I am trying to access my desktop application which is hosted on RDweb server from outside using browser “https://FQDN/RDweb” my RD gateway not forwarding my request to RDweb server. Kindly help me out how I can configure the forwarding, So when user hit my Rdweb url Rd gateway forward the same request to my Rd web and user can access the desktop application from browser.
Hi, I have been following this great guide, but run into problems with the certificates. Both Broker certificates and the one for Web Access display as “trusted”, but with “error”, saying: “Could not configure the certificate on one or more servers. Ensure that the servers are available on the network blah blah”. But these servers are the very one that the wizard runs on…
The certificate for the RD Gateway installs fine and works.
Any idea’s? Thanks!
i am following this procedure to creare a RemoteApps service only for publish a web browser app. I have a new virtual windows server to configure this RemoteApps service, but i don’t understand if this service have to be configured on a DC server or it is not necessary and i can configure it on some new other server. Thank you very much!
Hi,
I´ve got a problem:
the users must sign in doubled when accessing published apps from external PCs, over the rdgateway. One Login on the gateway and then a second time after clicking the RDP-File. Is there a solution?
“RemoteApp and Desktop Connections” in system settings :)
You can add your domain for the RD-Gateway there and all Apps and Desktops will appear in the start menu under “Work Resources”.
You have to do that on every external computer once and the user has to login only when creating the connection to the RD-Gateway.
Other than the Domain Controller, what other server could host the SQL database? Could it be put onto the RDS server? My current environment is a 2 DC 2 RDS environment for redundancy.
Nice Write.